Key Takeaways
A hacktivist used AI to expose web security flaws and delete sites live. Discover key takeaways for cybersecurity, data privacy, and ethical innovation.
Overview
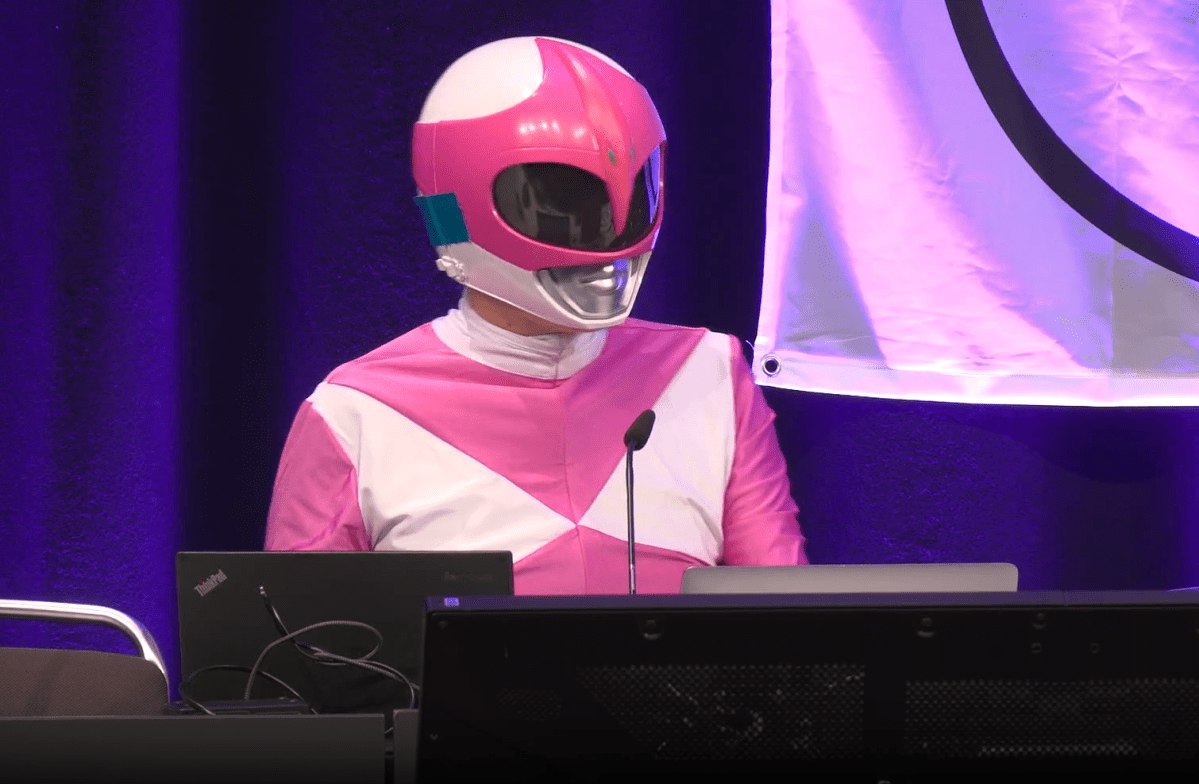
In a bold demonstration of digital activism, a hacktivist publicly wiped three white supremacist websites live on stage at the annual Chaos Communication Congress in Hamburg, Germany. This unprecedented act highlights the profound vulnerabilities even ideologically driven platforms face and showcases innovative methods in hacktivist operations, resonating strongly with the Technology India community.
For tech enthusiasts, innovators, and developers, this event underscores the critical importance of robust cybersecurity hygiene and the evolving landscape of digital defense. It also sparks discussions on ethical hacktivism and the use of AI in infiltration, a key area for startups and software development.
The pseudonymous hacker, “Martha Root,” dressed as Pink Ranger, deleted WhiteDate, WhiteChild, and WhiteDeal. The sites, described as a “Tinder for Nazis” and similar platforms, remain offline after the demonstration, revealing over 6,500 user profiles with precise geolocation metadata.
The incident forces a re-evaluation of web security best practices, particularly for platforms handling sensitive user data, and offers valuable insights into offensive security techniques that developers must understand to build resilient systems.
Key Data
| Website | Description | Key Vulnerability/Data | User Count (WhiteDate) |
|---|---|---|---|
| WhiteDate | “Tinder for Nazis” | Geolocation metadata in images, poor cybersecurity hygiene | >6,500 |
| WhiteChild | Sperm/egg donor matching | Infiltrated via AI chatbots, public data scraped | N/A |
| WhiteDeal | “Taskrabbit for racists” | Infiltrated via AI chatbots, public data scraped | N/A |
| User Demographics | WhiteDate Users | 86% Men, 14% Women | >6,500 |
Detailed Analysis
The act by “Martha Root” at the Chaos Communication Congress transcends a simple data breach; it represents a significant escalation in hacktivism, leveraging public spectacle and advanced techniques to achieve its goals. Historically, hacktivism has seen various forms, from distributed denial-of-service (DDoS) attacks to website defacements. However, the live, on-stage deletion of servers, coupled with prior data scraping and AI-driven infiltration, establishes a new benchmark for digital disruption. This development comes amid a broader trend of increasing digital vigilance against online extremism and misinformation, pushing the boundaries of what constitutes legitimate digital protest versus cyberterrorism, a debate now at the forefront for cybersecurity experts and legal scholars.
Root’s methodology offers a fascinating case study in modern offensive security. The pseudonymous hacker employed AI chatbots to bypass verification systems, a sophisticated approach that allowed infiltration into the white supremacist platforms. Once inside, Root exposed egregious cybersecurity flaws, noting “poor cybersecurity hygiene that would make even your grandma’s AOL account blush.” A critical finding was the presence of precise geolocation metadata embedded in user-uploaded images on WhiteDate, effectively revealing home addresses alongside user profiles. This level of data exposure, without basic security protocols like metadata stripping, highlights a fundamental disregard for user privacy and operational security. The scraped data included names, pictures, age, location, gender, language, and race, underscoring the depth of personal information collected and inadequately protected by these sites.
Comparing this incident to typical data breaches, the public nature and real-time execution distinguish it significantly. Most data breaches involve clandestine exfiltration, with public disclosure often occurring long after the fact. Root’s performance, however, transformed the act into a powerful statement, demonstrating immediate, irreversible consequences for the targeted infrastructure. This also contrasts with standard ethical hacking practices, which usually involve private disclosure to site administrators. The deliberate choice to publish the scraped data, now dubbed “WhiteLeaks” by DDoSecrets, and offer it to verified journalists and researchers, also aligns with a more activist-driven, transparency-focused approach, rather than solely financial gain often associated with cybercrime. The administrator’s claim of “cyberterrorism” versus the hacktivist’s view of “digital justice” frames a complex ethical dilemma relevant to the burgeoning field of cybersecurity innovation.
For tech enthusiasts, innovators, developers, and startup founders, this event offers several critical takeaways. Firstly, it’s a stark reminder that robust cybersecurity cannot be an afterthought; it must be ingrained from product inception, especially when handling sensitive user data. Secondly, the successful use of AI chatbots for infiltration points to the increasing sophistication of attack vectors, urging developers to integrate advanced AI-driven defenses and verification processes. Startup founders building new platforms, regardless of content, must prioritize data protection and privacy by design, learning from the “poor cybersecurity hygiene” that exposed thousands. The incident also highlights the evolving legal and ethical landscapes surrounding digital activism, where the line between legitimate protest and illicit activity remains hotly contested. Monitoring developments in AI-powered security solutions and data anonymization techniques will be crucial for building resilient and responsible digital ecosystems in India’s growing tech sector.