Key Takeaways
FBI probe into system admin’s classified data reveals critical data security risks. Explore implications for government IT, privacy, and future tech innovation for startups.
Overview
A recent FBI investigation involving a government system administrator has cast a critical spotlight on evolving data security risks and the profound responsibilities of technology professionals. This incident, centered on the unlawful retention of classified government materials, underscores the intricate challenges in information management and digital privacy for Technology India.
For Tech Enthusiasts, Innovators, Early Adopters, Developers, and Startup Founders, this probe highlights urgent considerations regarding digital footprints and the imperative for robust cybersecurity frameworks. It signals a growing scrutiny on how sensitive data is handled across all sectors.
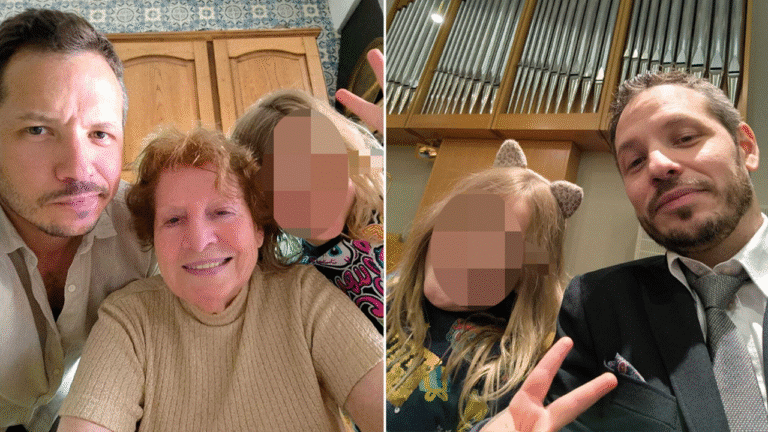
The investigation focuses on Aurelio Perez-Lugones, a system administrator with top secret security clearance since 2002, accused of retaining classified intelligence reports in unconventional places like a lunchbox and personal basement. The FBI also seized a Washington Post reporter’s personal devices, including a phone and Garmin watch, in connection to the case.
This development prompts a critical re-evaluation of security protocols and access management, urging close attention to emerging legal and ethical considerations in the innovation ecosystem.
Detailed Analysis
The intersection of national security with government contracting and individual digital privacy presents a multifaceted challenge for the contemporary tech landscape. Historically, safeguarding classified information has relied on stringent physical and digital access controls. However, this FBI probe brings to the forefront the human element as a potential vulnerability within these sophisticated systems. The role of a system administrator inherently involves privileged access to extensive networks and data. When this foundational trust is compromised, it exposes significant systemic weaknesses. For the broader innovation ecosystem, this incident serves as a potent reminder that even highly advanced technological safeguards can be undermined by individual actions or lapses in protocol, impacting data integrity and national security in an increasingly digitized world.
At the core of this investigation is Aurelio Perez-Lugones, a system administrator who has held top secret security clearance since 2002. The accusation that Perez-Lugones unlawfully accessed and retained classified government materials, discovered in seemingly innocuous locations like a lunchbox and personal basement, indicates severe breaches in established data handling protocols. For tech professionals, particularly those engaged in government or defense-related IT roles, this illuminates the stringent requirements and ethical obligations associated with privileged access. The seizure of a Washington Post reporter’s personal devices, including a phone and a Garmin watch, in direct connection to this probe further underscores the expanding scope of digital forensics and the increasingly blurred lines between professional conduct and personal digital lives. This has direct and significant implications for secure data practices, device management policies, and the overall cybersecurity posture within organizations entrusted with sensitive information.
This pivotal case resonates with broader industry trends concerning insider threats and the inherent vulnerabilities of remote work environments, where sensitive data may be handled with less security outside official premises. While specific market share or product comparison data is not detailed in this particular incident, the event stimulates a crucial comparative analysis of data encryption standards, access logging capabilities, and employee monitoring solutions deployed in government sectors versus private tech enterprises. Startups actively developing cybersecurity solutions for insider threat detection, secure communication platforms, and advanced data loss prevention (DLP) systems could foresee increased demand for their innovative offerings. Furthermore, this incident can be juxtaposed against general data protection regulations, such as India’s upcoming DPDP, which emphasize principles of data minimization and secure processing, even for non-classified information, highlighting a universal need for robust security postures.
For Tech Enthusiasts, Innovators, Developers, and Startup Founders, this incident serves as a critical real-world case study on the tangible implications of cybersecurity lapses and digital ethics. It emphasizes the paramount importance of implementing robust access management strategies, secure data storage practices, and strict adherence to established protocols, especially for professionals involved in government contracting or handling any form of sensitive data. Startups focusing on next-generation authentication mechanisms, end-to-end encrypted communication tools, or decentralized and immutable data storage solutions could discover fertile ground for growth as organizations seek to prevent similar breaches. Developers should proactively integrate secure-by-design principles into all applications, particularly those engineered to handle confidential information. Upcoming policy debates surrounding journalistic privacy in the digital age and enhanced regulatory frameworks for government contractors managing sensitive data are key metrics to continuously monitor. This incident starkly reminds us that the human element often remains the weakest link in even the most secure technological chains, underscoring the ongoing necessity for innovation in human-centric security solutions.